Blogs
Mike try a contribute defense reviewer from the Upcoming, in which he be concerned-examination VPNs, anti-virus and a lot more to determine and that characteristics are certain to keep you safe, and which happen to be better avoided. The guy talks about all things cybersecurity, and id theft, ransomware, and you will study breaches, along with laws linked to industry. In which you can, we checked the newest programs on a single platforms to make sure i created a good assessment but we and checked how the overall performance of specific apps varied from system to platform. After we’ve make a summary of software programs, it’s returning to the new assessment to start. Establishing parental control utilizes the device brands and doing work systems you and your family have fun with.
- That it isn’t an accurate research, and there’s no number you can undergo to state that an software is actually definitively dependable or untrustworthy.
- Louis DeNicola is actually self-employed individual fund and you may credit blogger which work that have Luck 500 monetary features firms, FinTech startups, and you will low-payouts to educate somebody on the currency and borrowing.
- Evaluate app permissions, ratings, and you will creator character.
- A short time later, 17 of the apps been contacting an identical malware server.
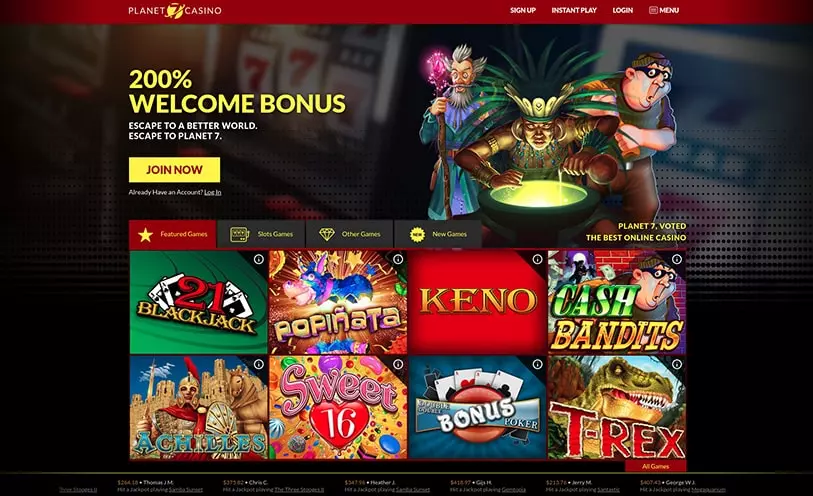
Greatest Games on the net
They can spread trojan, bargain analysis because of phishing strategies, and you will set up unwelcome software, such as adware or https://vogueplay.com/in/the-sword-and-the-grail-slot/ malware. Bogus installer applications replicate legitimate installer programs to have common software. Bogus banking software echo the appearance and you can capabilities of really-identified banking software. Phony text message apps appear because the legitimate safe messaging services such as WhatsApp or Signal.
- While you are not to ever blame when someone behaves inside a predatory otherwise disrespectful ways to your your on the dating world, there are things you can do to keep safe.
- Profiles can feel self assured this software program is legitimate and you will safe should your name is identifiable and you can section of a reliable brand.
- Light standards gamble a serious role from the development of their crape myrtle.
- The video game symbol will act as an untamed, while you are Thor’s hammer – Mjölnir – is the spread.
Interactive tale or simulation software might possibly be issues
What’s more, it brings a dysfunction of the kid’s hobby on the internet, like the web sites they view, apps they use, and you may social network postings they generate. I became and amazed because of the cyberbullying notification, which ping your if the application finds abusive text or sound chats from online Desktop game, which is run on ProtectMe, a third-people offering of Kidas. I found you to installing the new parental handle piece try quick plus the software simple to use, delivering a great QR password to help you download for added comfort. You’re not merely delivering a parental manage application but also identity security, antivirus, VPN, code movie director, and. He’s got a love of protection products that continue somebody secure, and also the education to enable them to make the correct choice. Benedict has invested over 7 years discussing defense items, coating everything from big study breaches and you can cyber symptoms, on the trojan and you can credentials thefts you to definitely jeopardize livelihoods and private protection.
Programs that need you to agree to plenty of a lot more posts was trying to steal your computer data. In case your application presents your with fine print once you unlock it, realize her or him. So they allow you to agree to analysis exploration, analysis sharing, pop-ups, and all types of other things. These types of sly designers remember that the majority of people tend to mouse click “Accept” rather than understanding. Should your creator try imitating more popular issues or saying their application are a reduced variation, usually do not simply click! An authorization are suspicious should your app cannot list any function who does are interested.
Basketball Video game
“Our very own studies show zero Bluetooth sex toys you to pertain secure ‘bonding’ when hooking up to a phone. “Also simply beginning the fresh Bluetooth explorer on the cellular phone can tell you nearby wise adult devices which might be powered for the.” Researchers observe that dated brands from Bluetooth that have been quit on account of shelter dangers are often nonetheless put. Bluetooth are a repeating discomfort section for IoT protection. Researchers provides demonstrated just how easy it’s to help you cheat to your common points time and again.
Phony game applications
Thunderstruck featuring Kevin Durant, Taylor Grey, Jim Belushi, Brandon T. Jackson have a great PG score, a great runtime around step one hours 34 minute. Delight logout and then sign on once more, then you will be encouraged to go into your screen identity. He’s in addition to kept numerous modules to the content writing to have Portray Communication.
What is actually Scareware? Revealing Signs & Tips Eliminate it
Rose done the brand new Material or Tits Globe Tour that have Air-con/DC, only to later register Ac/DC fulltime which have Angus More youthful declaring a desire for tape another record album that have Rose. Moving Brick’s comment included the new report “Hard rock provides unquestionably hit the all the-go out low.” You want any assist cleaning you to eggs out of your head, Rolling Stone? Within the 2004, AC/DC ranked 72 to the Running Brick’s listing of the best one hundred musicians ever.